Hi,
I have OD 1.13.2 deployed in a kubernettes cluster. All configs are done with configmaps and mounted in the pods upon boot. eg: roles.yml, roles_mapping.yml, etc
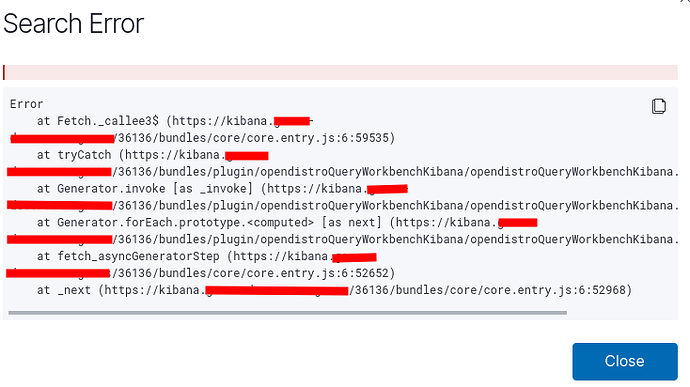
Users connect via LDAP which works just fine. My problem is that only the admin can download reports. Not sure if it is because of tenants, or if I am just not understanding the flow correctly. Below are my config files. Any help would be much appreciated.
Regards
config.yml: |-
_meta:
type: "config"
config_version: 2
config:
dynamic:
authc:
basic_internal_auth_domain:
http_enabled: true
transport_enabled: false
order: 2
http_authenticator:
type: basic
challenge: true
authentication_backend:
type: internal
ldap:
description: "Authenticate via LDAP or Active Directory"
http_enabled: true
transport_enabled: true
order: 1
http_authenticator:
type: basic
challenge: true
authentication_backend:
type: ldap
config:
enable_ssl: true
enable_start_tls: false
enable_ssl_client_auth: false
verify_hostnames: false
hosts:
- ldap.redacted.com:636
bind_dn: "CN=redacted_user,OU=Generic,OU=ServiceAccounts,OU=Users,OU=Anzo,DC=corp,DC=redacted,DC=com"
password: "redacted"
userbase: "OU=Users,OU=Anzo,DC=corp,DC=redacted,DC=com"
usersearch: '(SAMACCOUNTNAME={0})'
username_attribute: "SAMACCOUNTNAME"
authz:
roles_from_myldap:
http_enabled: true
transport_enabled: true
authorization_backend:
type: ldap
config:
enable_ssl: true
enable_start_tls: false
enable_ssl_client_auth: false
verify_hostnames: false
hosts:
- ldap.redacted.com:636
bind_dn: "CN=redacted_user,OU=Generic,OU=ServiceAccounts,OU=Users,OU=Anzo,DC=corp,DC=redacted,DC=com"
password: "redacted"
userbase: "OU=Users,OU=Anzo,DC=corp,DC=redacted,DC=com"
usersearch: '(uid={0})'
username_attribute: null
rolebase: 'OU=Kibana,OU=Applications,OU=Groups,OU=Anzo,DC=corp,DC=redacted,DC=com'
rolesearch: '(member={0})'
userrolename: 'memberOf'
resolve_nested_roles: true
rolename: "cn"
skip_users:
- "kibanaserver"
- "admin"
roles_mapping.yml: |-
# In this file users, backendroles and hosts can be mapped to Open Distro Security roles.
# Permissions for Opendistro roles are configured in roles.yml
_meta:
type: "rolesmapping"
config_version: 2
# Define your roles mapping here
all_access:
reserved: false
backend_roles:
- "admin"
- "sec.gg.kibana-admin" #<-------- LDAP admin group
description: "Maps admin to all_access"
ldap_user:
reserved: false
backend_roles:
- "sec.gg.kibana-ro" #<-------- LDAP Read Only Group
- "sec.gg.kibana-wl-noc-ro" #<-------- LDAP Read Only Group
users:
- "*"
description: "Maps ldap users to ldap_users"
kibana_user:
reserved: false
backend_roles:
- "kibanauser"
users:
- "*"
description: "Maps kibanauser to kibana_user"
own_index:
reserved: false
users:
- "*"
description: "Allow full access to an index named like the username"
roles.yml: |-
_meta:
type: "roles"
config_version: 2
sec.gg.kibana-ro: #<------- LDAP RO Group role
reserved: false
cluster_permissions:
- 'cluster_all'
- 'indices_all'
- 'cluster:admin/opendistro/reports/definition/create'
- 'cluster:admin/opendistro/reports/definition/update'
- 'cluster:admin/opendistro/reports/definition/on_demand'
- 'cluster:admin/opendistro/reports/definition/delete'
- 'cluster:admin/opendistro/reports/definition/get'
- 'cluster:admin/opendistro/reports/definition/list'
- 'cluster:admin/opendistro/reports/instance/list'
- 'cluster:admin/opendistro/reports/instance/get'
- 'cluster:admin/opendistro/reports/menu/download'
index_permissions:
- index_patterns:
- "*"
allowed_actions:
- '*'
tenant_permissions:
- tenant_patterns:
- "*"
allowed_actions:
- "*"
static: false
sec.gg.kibana-wl-noc-ro: #<------- LDAP RO Group role
reserved: false
cluster_permissions:
- 'cluster_all'
- 'indices_all'
- 'cluster:admin/opendistro/reports/definition/create'
- 'cluster:admin/opendistro/reports/definition/update'
- 'cluster:admin/opendistro/reports/definition/on_demand'
- 'cluster:admin/opendistro/reports/definition/delete'
- 'cluster:admin/opendistro/reports/definition/get'
- 'cluster:admin/opendistro/reports/definition/list'
- 'cluster:admin/opendistro/reports/instance/list'
- 'cluster:admin/opendistro/reports/instance/get'
- 'cluster:admin/opendistro/reports/menu/download'
index_permissions:
- index_patterns:
- "*"
allowed_actions:
- '*'
tenant_permissions:
- tenant_patterns:
- "*"
allowed_actions:
- "*"
static: false
...
...
elasticsearch.yml: |-
_meta:
type: "config"
config_version: 2
cluster.name: "elasticsearch"
network.host: 0.0.0.0
# # minimum_master_nodes need to be explicitly set when bound on a public IP
# # set to 1 to allow single node clusters
# # Details: https://github.com/elastic/elasticsearch/pull/17288
# discovery.zen.minimum_master_nodes: 1
# # Breaking change in 7.0
# # https://www.elastic.co/guide/en/elasticsearch/reference/7.0/breaking-changes-7.0.html#breaking_70_discovery_changes
# cluster.initial_master_nodes:
# - elasticsearch1
# - docker-test-node-1
# xpack.security.enabled: false
# xpack.monitoring.enabled: false
######## Start OpenDistro for Elasticsearch Security Demo Configuration ########
# WARNING: revise all the lines below before you go into production
opendistro_security.ssl.transport.pemcert_filepath: esnode.pem
opendistro_security.ssl.transport.pemkey_filepath: esnode-key.pem
opendistro_security.ssl.transport.pemtrustedcas_filepath: root-ca.pem
opendistro_security.ssl.transport.enforce_hostname_verification: false
opendistro_security.ssl.http.enabled: true
opendistro_security.ssl.http.pemcert_filepath: esnode.pem
opendistro_security.ssl.http.pemkey_filepath: esnode-key.pem
opendistro_security.ssl.http.pemtrustedcas_filepath: root-ca.pem
opendistro_security.allow_unsafe_democertificates: true
opendistro_security.allow_default_init_securityindex: true
opendistro_security.authcz.admin_dn:
- CN=kirk,OU=client,O=client,L=test, C=de
opendistro_security.multitenancy.enabled: true
opendistro_security.multitenancy.enable_filter: true
opendistro_security.multitenancy.tenants.preferred: ["Global"] #<---- Only use one tenant for all
opendistro_security.multitenancy.tenants.enable_private: false #<--- Do not use private tenenat
# server.defaultRoute: /?security_tenant=global
opendistro_security.roles_mapping_resolution: BOTH
opendistro_security.audit.type: internal_elasticsearch
opendistro_security.enable_snapshot_restore_privilege: true
opendistro_security.check_snapshot_restore_write_privileges: true
opendistro_security.restapi.roles_enabled: ["all_access", "security_rest_api_access"]
opendistro_security.system_indices.enabled: true
opendistro_security.system_indices.indices: [".opendistro-alerting-config", ".opendistro-alerting-alert*", ".opendistro-anomaly-results*", ".opendistro-anomaly-detector*", ".opendistro-anomaly-checkpoints", ".opendistro-anomaly-detection-state", ".opendistro-notifications-*", ".opendistro-reports-*"]
cluster.routing.allocation.disk.threshold_enabled: false
node.max_local_storage_nodes: 1
######## End OpenDistro for Elasticsearch Security Demo Configuration ########
kibana.yml: |-
server.name: kibana
server.host: "0"
elasticsearch.hosts: https://localhost:9200
elasticsearch.ssl.verificationMode: none
elasticsearch.username: kibanaserver
elasticsearch.password: kibanaserver
elasticsearch.requestHeadersWhitelist: ["securitytenant","Authorization"]
opendistro_security.basicauth.login.brandimage: "https://redacted.com/wp-content/uploads/2020/02/logo-04-1.png"
opendistro_security.basicauth.login.title: "Welcome to...redacted"
opendistro_security.basicauth.login.subtitle: To log in use your LDAP account and password
opendistro_security.multitenancy.enabled: true
opendistro_security.multitenancy.enable_filter: true
opendistro_security.multitenancy.tenants.preferred: ["Global"]
opendistro_security.multitenancy.tenants.enable_private: false
opendistro_security.readonly_mode.roles: ["kibana_read_only"]
# Use this setting if you are running kibana without https
opendistro_security.cookie.secure: false
newsfeed.enabled: false
telemetry.optIn: false
telemetry.enabled: false
security.showInsecu^eClusterWarning: false